365 One Drive Business Setting up Synchronization

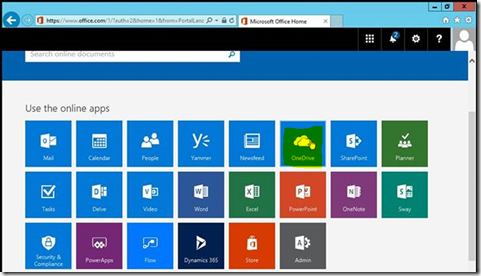
Create a separate One Drive “Cloud Administrator” account and assign a 365 license to the account. From the file server open Http://portal.office.com and log on using the Cloud Administrator account Once logged on select One Drive as shown below: Once it sets up your One Drive you can select “Your OneDrive is ready” In the OneDrive Menu select Sync as shown below: Click Allow this website to open an app: It will pop up the following “Getting Ready to sync…” if nothing happens or if you get prompted that you need an app. Then it does not have the proper version already on the system you may have to click on “Get the latest version of OneDrive as: You should then see the following to enter in your Cloud Admin account and sign in: You will get prompted with a password logon for Office 365 which will require that same account Sign in. Then you will see the following which we will redirect to the folder we want to sync by selecting “Change Location” In this case I will go to the D:\...